Friday, May 22, 2020
Thursday, May 21, 2020
RED_HAWK: An Information Gathering, Vulnerability Scanning And Crawling Tool For Hackers
About RED_HAWK: RED_HAWK is a all in one tool for Information Gathering, Vulnerability Scanning and Crawling. A must have tool for all pentesters and hackers.
RED_HAWK's features:
- Basic ScanSite Title (NEW):
IP Address
Web Server Detection IMPROVED
CMS Detection
Cloudflare Detection
robots.txt Scanner - Whois Lookup (IMPROVED)
- Geo-IP Lookup
- Grab Banners IMPROVED
- DNS Lookup
- Subnet Calculator
- Nmap Port Scan
- Sub-Domain Scanner IMPROVED:
Sub Domain
IP Address - Reverse IP Lookup and CMS Detection IMPROVED:
Hostname
IP Address
CMS - Error Based SQLi Scanner
- Bloggers View NEW
HTTP Response Code
Site Title
Alexa Ranking
Domain Authority
Page Authority
Social Links Extractor
Link Grabber - WordPress Scan NEW
Sensitive Files Crawling
Version Detection
Version Vulnerability Scanner - Crawler
- MX Lookup NEW
- Scan For Everything - The Old Lame Scanner
- WordPress
- Joomla
- Drupal
- Magento
How To Configure RED HAWK with moz.com for Bloggers View Scan?
- Create an account in moz follow this link: Register New Community Account - Moz
- After successful account creation and completing the verification you need to generate the API Keys.
- You can get your API Keys here: https://moz.com/products/mozscape/access.
- Get your AccessID and SecretKey and replace the
$accessIDand$secretKeyvariable's value in theconfig.phpfile
How to use RED_HAWK?
Known Issues of RED_HAWK
ISSUE: Scanner Stops Working After Cloudflare Detection!
SOLUTION: Use the
fix command (for Debian-based distros) or manually install php-curl and php-xml.Watch the video to see how to solve that isuue:
Support and Donations
Found RED_HAWK cool? Well you could buy a cup of tea for the author 😉 Just send any amount of donations (in Bitcoin) to this address: 1NbiQidWWVVhWknsfPSN1MuksF8cbXWCku
Can't donate? well that's no problem just drop a "THANK YOU, AUTHOR" this will motivate me to create more exciting stuffs for you 😉
TODOs for RED_HAWK:
- Make a proper update option ( Installs current version automatically )
- Add more CMS to the detector
- Improve The WordPress Scanner ( Add User, Theme & Plugins Enumeration )
- Create a web version of the scanner
- Add XSS & LFI Scanner
- Improve the Links grabber thingy under bloggers view
- Add some other scans under the Bloggers View
Related word
How To Download Torrents Files Directly To Your Android Device
Procedure:
- Download and install uTorrent on your smartphone or tablet
- At the end of the installation click Open.
- Look for the torrents of your choice, several free and legal resources are available:
- http://www.legittorrents.info/
- http://www.publicdomaintorrents.info/
- http://www.legaltorrents.com/
- In the list of results, click on the magnet shaped button that appears below the file you want to download
- A window showing where the file will be saved in the memory card will open. Click on Add
- Utorrent will start downloading the file
- Once the download is complete press the Play button to open the file
Other softwares
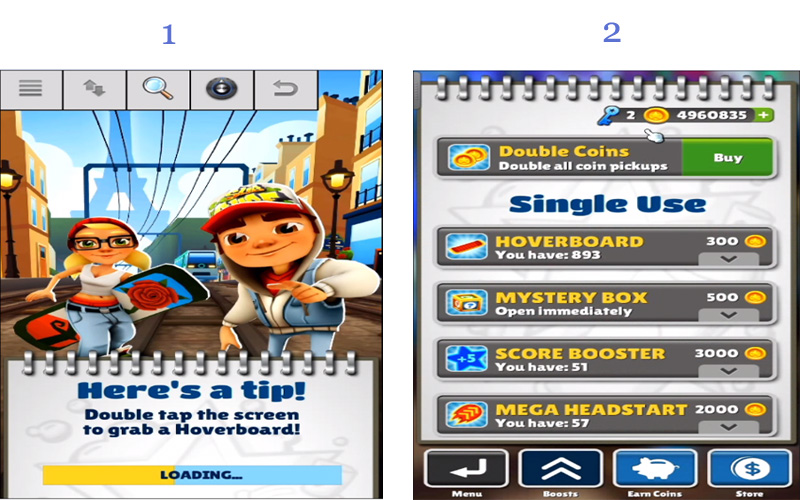
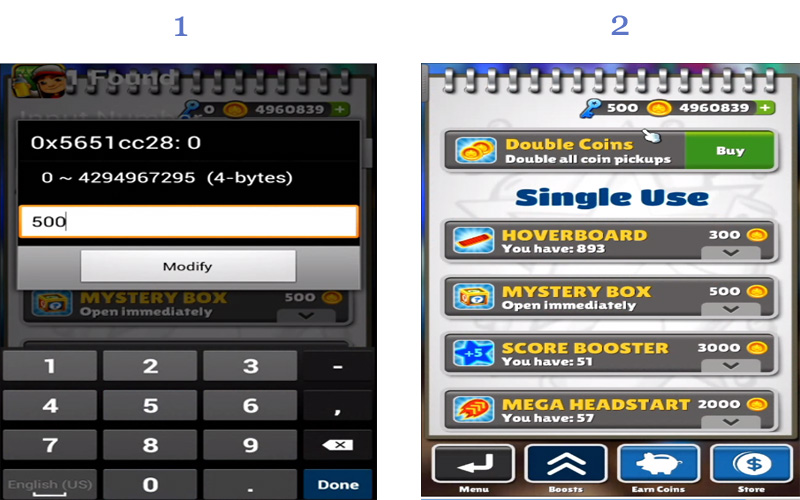
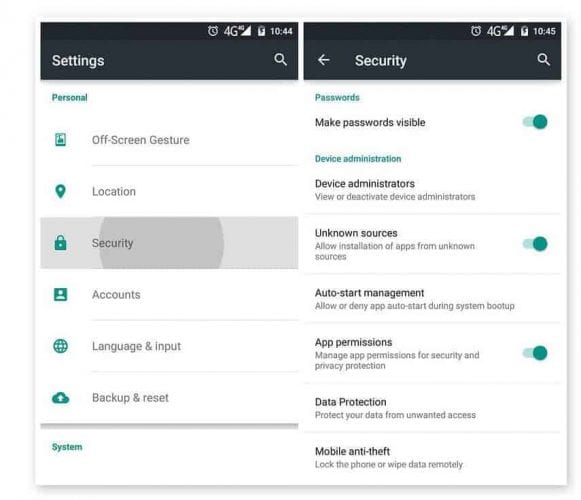
How To Hack Any Game On Your Android Smartphone

How To Hack Any Game On Android 2018
Steps To Hack Any Game On Android
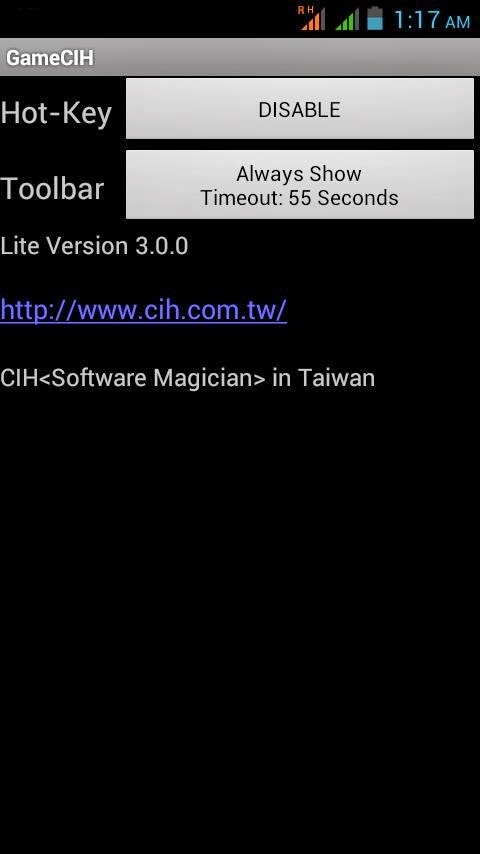
Using Game Guardian
Related articles
Linux Command Line Hackery Series - Part 5

Welcome back to the Linux Command Line Hackery series, this is Part-V of the series. Today we are going to learn how to monitor and control processes on our Linux box, so wrap your sleeves up and let's get started.
Command: ps
Syntax: ps [options]
Description: ps displays information about the currently running processes. Some of the common flags of ps are described briefly below
Flags:
-A or -e -> select all processes
-a -> select all processes except both session leaders and processes not associated with a terminal.
T -> select all processes associated with current terminal
-u <username or id> -> select all processes of a given user or userlist
Open up a terminal and type ps:
ps
what you'll see is a list of processes currently running in your terminal. One important thing to notice in the output is what's called as PID which stands for process ID. It is the number that uniquely identifies a process. Just keep that PID concept in mind we'll use it soon.
OK I know that's not really what you want to see rather you want to see all the processes that are currently running on your box. Don't worry we have flags to rescue, in order to see all the processes you can use the -e flag like this:
ps -e
Boom! you get a long list of processes currently running on your machine (don't stare at me like that, you asked and I gave you that). If you want to see processes of a particular user you can type the following command in your terminal:
ps -u bob
here "bob" is a username. This command will list all processes of the user with effective user name of bob.
You can do a full-format listing of the processes using the -f flag like this:
ps -fu bob
But the output of the ps command is a snapshot not really a live preview of what is going on in your box. I know your next question is going to be something like this, Isn't there a command in Linux that gives me a live updating information of the processes? Yes, there is a command called top that we'll learn about next.
Command: top
Syntax: top [options]
Description: top gives a dynamic real-time view of a running system. That is, it gives the up-to-date information about all the processes running on your Linux box (sounds fun!). Besides giving information about current processes and threads top also provides a brief system summary.
To start top just type this command:
top
and you'll get a nice and cute looking ugly display :). Well what the heck is going on here you might ask, right? What you get is information about what is going on with your computer. To see what more can you do with top just type <h> within the program window and you'll be given list of options that you can play with.
OK looking at what processes are going on in your box is cool but what if you want to terminate (or close) a process, is there a command line utility for that? Yes, there is and that's what we are going to look at next.
Command: kill
Syntax: kill [options] <pid> [...]
Description: kill is used to send a signal to process which by default is a TERM signal meaning kill by default sends a signal of termination to process (Cruel guy). To list the available signals we can use the -l or -L flag of the kill command.
To simply terminate a process we provide kill command a PID (process ID) and it will send the TERM signal to the process. So to kill a process first we'll list the running processes and then we'll keep the PID of the process in mind that we want to terminate. After that we'll issue the kill command with the PID that we just found.
ps -ax
kill 1153
the above command will send a TERM signal to the process whose PID is 1153, as simple as that.
We can also use our already learned skills to refine the output of ps command. Say we have a xterm terminal running on our box and we want to terminate it. By using ps command all alone we'll get a long listing of all processes running on our box. But we can limit the output of ps command to just those processes that we're interested in by piping ps command with the grep command like this:
ps -ax | grep xterm
wow! that's amazing, we're able to pull out only those results from the ps command that contained xterm in them. Isn't that a cool trick? But what is that vertical bar ( | ) doing in the middle, you may be thinking, right? Remember we learned about the input and output re-directors previously, the vertical bar (pipe in geeky terms) is another re-director whose task is to redirect the output of one command as input to another command. Here the pipe redirects the output of ps -ax command as input to grep command and of-course from the previous article you know that grep is used to search for a PATTERN in the given input. That means the above command searches for the xterm word in the output of ps -ax command and then displays just those lines of ps -ax command which contain xterm. Now get that PID and kill that process.
That's it for today, try these commands up on your own box and remember practice is gonna make you master the Linux command line. :)
Related posts
TERMINOLOGIES OF ETHICAL HACKING
What is the terminologies in ethical hacking?
Here are a few key terms that you will hear in discussion about hackers and what they do:
1-Backdoor-A secret pathway a hacker uses to gain entry to a computer system.
2-Adware-It is the softw-are designed to force pre-chosen ads to display on your system.
3-Attack-That action performs by a attacker on a system to gain unauthorized access.
4-Buffer Overflow-It is the process of attack where the hacker delivers malicious commands to a system by overrunning an application buffer.
5-Denial-of-Service attack (DOS)-A attack designed to cripple the victim's system by preventing it from handling its normal traffic,usally by flooding it with false traffic.
6-Email Warm-A virus-laden script or mini-program sent to an unsuspecting victim through a normal-looking email message.
7-Bruteforce Attack-It is an automated and simplest kind of method to gain access to a system or website. It tries different combination of usernames and passwords,again & again until it gets in from bruteforce dictionary.
8-Root Access-The highest level of access to a computer system,which can give them complete control over the system.
9-Root Kit-A set of tools used by an intruder to expand and disguise his control of the system.It is the stealthy type of software used for gain access to a computer system.
10-Session Hijacking- When a hacker is able to insert malicious data packets right into an actual data transmission over the internet connection.
11-Phreaker-Phreakers are considered the original computer hackers who break into the telephone network illegally, typically to make free longdistance phone calls or to tap lines.
12-Trojan Horse-It is a malicious program that tricks the computer user into opening it.There designed with an intention to destroy files,alter information,steal password or other information.
13-Virus-It is piece of code or malicious program which is capable of copying itself has a detrimental effect such as corrupting the system od destroying data. Antivirus is used to protect the system from viruses.
14-Worms-It is a self reflicating virus that does not alter files but resides in the active memory and duplicate itself.
15-Vulnerability-It is a weakness which allows a hacker to compromise the security of a computer or network system to gain unauthorized access.
16-Threat-A threat is a possible danger that can exploit an existing bug or vulnerability to comprise the security of a computer or network system. Threat is of two types-physical & non physical.
17-Cross-site Scripting-(XSS) It is a type of computer security vulnerability found in web application.It enables attacker to inject client side script into web pages viwed by other users.
18-Botnet-It is also known as Zombie Army is a group of computers controlled without their owner's knowledge.It is used to send spam or make denial of service attacks.
19-Bot- A bot is a program that automates an action so that it can be done repeatedly at a much higher rate for a period than a human operator could do it.Example-Sending HTTP, FTP oe Telnet at a higer rate or calling script to creat objects at a higher rate.
20-Firewall-It is a designed to keep unwanted intruder outside a computer system or network for safe communication b/w system and users on the inside of the firewall.
21-Spam-A spam is unsolicited email or junk email sent to a large numbers of receipients without their consent.
22-Zombie Drone-It is defined as a hi-jacked computer that is being used anonymously as a soldier or drone for malicious activity.ExDistributing Unwanted Spam Emails.
23-Logic Bomb-It is a type of virus upload in to a system that triggers a malicious action when certain conditions are met.The most common version is Time Bomb.
24-Shrink Wrap code-The process of attack for exploiting the holes in unpatched or poorly configured software.
25-Malware-It is an umbrella term used to refer a variety of intrusive software, including computer viruses,worms,Trojan Horses,Ransomeware,spyware,adware, scareware and other malicious program.
Follow me on instagram-anoymous_adi
Wednesday, May 20, 2020
Leo's Noob
I would like to send a salve to my friend noob at Rivendel in Brazilian company hahaha
Tuesday, May 19, 2020
Difference Between Hacker, Programmer, And Developer
There are numerous sprite debates and discussions on the differences between hackers, developers, and programmers. With most descriptions, however, there is usually a slight flaw in at least one or two serious ways. These terms are all traditionally misused and misunderstood, with many of us frequently mixing them up as an all-encompassing definition of anyone working on the Software realm.
However, if you are looking to clarify your project goals and business needs adequately, it is essential that you understand that all these terms do not all represent the same thing (although a person with the ability to program a computer can use different skills to accomplish various outcomes).
What's more, it is also quite important for you to differentiate between these three terms if you are working with software development groups and the fact that they cannot be interchanged. This excerpt seeks to break it all down for you mainly-the vital difference between hackers, developers, and programmers, their actual tasks, as well as their relationship.
The Hacker
A hacker is a computer expert who uses his knowledge of computer networking, programming, cryptography, and databases to overcome a problem in the system. Hackers are more concerned with availing the concept as opposed to minding about the long-term quality. And although a hacker can conceptualize about how will ultimately be created while frantically writing code, the role is primarily about speed.
A hacker, as well as hacking,' are most useful in dealing with emergency circumstances or when prototyping an item. Hackers and the profession of hacking, in general, is not concerned with the ultimate effect of the code.
Hackers make things. They typically alter the things programmers create and transform them to function differently as well as also writing codes. While "hacker" can refer to any skilled technical person, the term has become associated with computer security, someone who, with their technical knowledge, uses bugs or exploits to break into computer systems.
The Programmer
A programmer is an individual equipped with the expertise to write codes. Programmers usually master in a single or multiple programming languages and boast vast knowledge on related areas also. Their roles are relatively procedural and mandate for total concentration not to mention refined skills.
A programmer is solely focused both in writing codes as well as getting features appropriately performed so that these features are accessible for integration and later use. Programming is merely the process of swinging the hammer and adequately creating the software.
Usually, it is easy to identify that an individual is in programming mode since they often have a concentrated gaze and are deep in the zone.' Programmers are normally internalizing the system they are operating as well as editing and writing pieces of something that can only best be described as a long algebra problem.'
The Developer
Developers are typically creators. However, not anyone that is an expert at writing codes can be a developer. Developers are experts at identifying ways around various problems as well as plugging together components to fulfill some requirements. These professionals solve problems or create things by adhering to a specific set of principles (design and implementation).
This set of principles includes attributes such as maintainability, performance, robustness, security, and scale among others. They solve problems in a systematic manner. Ideally, this is what distinguishes programmers, developers, and hackers.
In A Nutshell:
In all simplicity, these three professionals solve various problems using code. A programmer is an encompassing term that means a problem solver, a developer is a trained programmer (formal) who besides resolving issues achieves it in an organized and methodical manner likely instilled in the course of their formal education, and a hacker is a tinkerer/creator.
Despite their differences in individual meaning and professional capacities, these terms, however, can interrelate with each other quite effectively. In fact, it is possible for you to combine the skills to your benefit. In reality, all developers and hackers are programmers. However, despite their expertise, not many developers and programmers are creative enough to warrant an identity as hackers.
Finally, although hackers and programmers are quite impressive, they are however not experienced or educated enough to warrant consideration as developers. The similarity, however, is that all work to create code, each in their specified manner.
Ideally, anyone would work to be all the above-as creative as a hacker, though, somewhat better experienced and formally trained to design software as opposed to only hacking.
Nonetheless, even if you lack the creativity, experience, or education, or either to necessarily create a broad application, it is still worth noting that you are still ideally a programmer. And in case you did not know, solving a problem through code is by itself, a superpower!
@£√£RYTHING NT
More articles
MyPublicInbox: Algunos Perfiles Públicos Del Mundo Del Empredimiento Y La Cultura #MyPublicInbox @Mypublicinbox1
 |
| Figura 1: MyPublicInbox: Algunos Perfiles Públicos del mundo del Empredimiento y la Cultura |
 |
| Figura 2: Contactar con Fernando Romay en MyPublicInbox |
 |
| Figura 3: Contactar con Willy Barcenas en MyPublicInbox |
 |
| Figura 4: Contactar con Covadonga Fernández |
 |
| Figura 5: Contactar con José Fernando Molina Pinos en MyPublicInbox |
 |
| Figura 6: Contactar con Lorenzo Caprile en MyPublicInbox |
 |
| Figura 7: Contactar con Polo Villaamil en MyPublicInbox |
Andrés Ortiz Moyano
 |
| Figura 8: #Yihad: Cómo el estado islámico ha conquistado inernet y los medios de comunicación. |
 |
| Figura 9: Contactar con Andrés Ortiz Moyano |
Teresa Gonzalo
 |
| Figura 10: Contactar con Teresa Gonzalo |
 |
| Figura 11: Contactar con José Antonio Germán |
 |
| Figura 12: Contactar con Jesús V. Sánchez-Bermejo |
- MyPublicInbox: Campaña contra el Coronavirus
- MyPublicInbox: Muchos más perfiles públicos
- Cómo establecer relaciones profesionales y obtener respuesta gracias a MyPublicInbox
- ¡El e-mail ha muerto! ¡Larga vida al e-mail!
- MyPublicInbox: Milestone ZERO
- MyPublicInbox: Servicio de Originales Digitales
- MyPublicInbox: La española que puede competir con Linkedin
- MyPublicInbox: Haz que te paguen por leer tu correo
- MyPublicInbox: Cuando 24 horas al día no son suficientes
- [Youtube]: MyPublicInbox por Chema Alonso